PS4: Crypto Coprocessor kernel exploit by flat_z, allows dump of SAMU keys
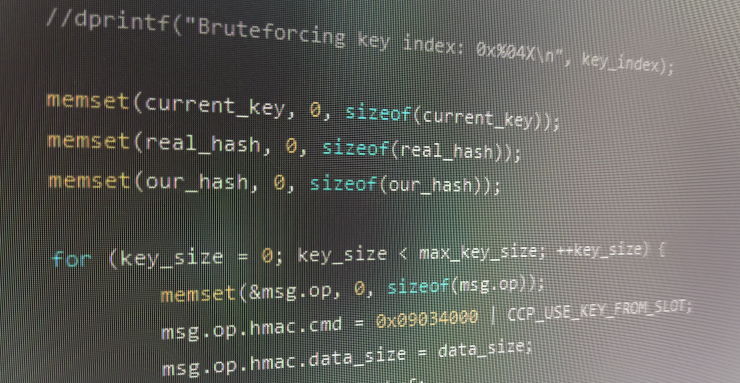
Scene veteran developer Flat_z has disclosed a PS4 Crypto Coprocessor (CCP) exploit, which impacted all models but has been patched by Sony somewhere between Firmwares 7.55 and 9.00.
According to the hacker, this exploit has allowed hackers to dump multiple keys from the PS4 through bruteforce, including AES/HMAC keys from PFS, portability keys, VTRM keys, and more.
Wait, what do I do with this?
If you own a console on firmware 7.51 or lower, you might be able to compile this code and run it on a Jailbroken PS4, to acquire some keys specific to your console.
Now, the actual usefulness of these keys is being heavily debated on the scene, with most people, including some people who have been on the scene for a while, not being sure what can be done with the keys. Let’s face it: unless you’ve been diving into firmware reverse engineering and/or homebrew programming for a while on the PS4, you won’t know what each type of key can, or cannot do.
At the very least, PFS keys could be used to decrypt game packages, and Flat_z has stated save files can be decrypted as well.
In any case all of these are decryption (not encryption) keys, so this cannot be used (in isolation, at least) to fulfill your dreams of a permanent CFW on the PS4.
Download
You can get the source for the exploit on the developer’s github, here.